How a Price Manipulation Attack Hit Our Vault — and What We Built to Stop It
An attacker exploited a Polymarket CLOB vulnerability to create fake price spikes and drain vault capital. Here's the full breakdown and the TWAP guard we shipped in hours.

Last weekend, an attacker exploited a known vulnerability in hybrid CLOB (Central Limit Order Book) architecture to manipulate prices on markets listed on Ultramarkets. The attack caused approximately $3,200 in bad debt to our vault across multiple incidents. We identified the attack vector, shipped a mitigation within hours, seized $1,050 in attacker funds still on the platform, and banned the account.
This post explains what happened, how the exploit works, what we built to stop it, and what it means for the vault and for traders.
What Happened
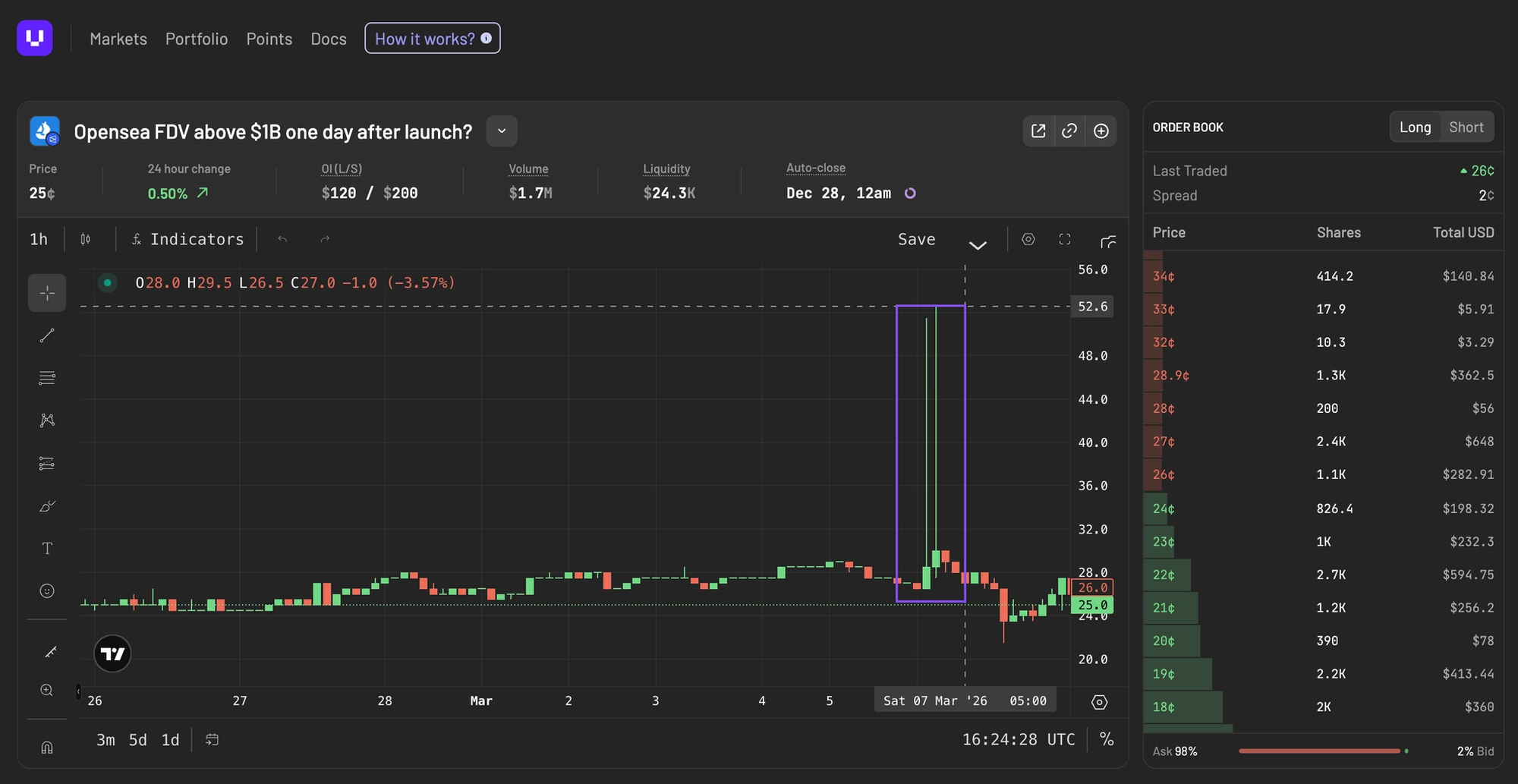
On March 6-7, we observed a pattern: a user was opening leveraged positions at prices wildly inconsistent with the market's actual trading range, and those positions were immediately liquidating. The vault was absorbing losses each time.
The first incident cost the vault roughly $3,000. A second incident on March 7 cost another ~$200. The pattern was identical both times: a momentary price spike on the underlying CLOB that vanished within seconds, combined with a leveraged position opened at precisely the inflated price.
This was obviously not a bad trade. In fact, it was a deliberate attack.
How the Exploit Works
Hybrid CLOBs, used across prediction markets and other trading venues, match orders off-chain for speed and settle on-chain for security. This design enables low-latency trading and tight spreads, but it creates a timing gap between when a trade is matched and when it finalizes on-chain.
A known class of attacks exploits this gap. DeFi Rate documented the issue in detail, describing how attackers submit orders that match off-chain but are designed to fail during on-chain settlement. The result is temporary price dislocations, often called "ghost fills," where the order book reflects a price that never actually settled.
In the variant that hit us, the attacker created brief, artificial price spikes on specific markets. These spikes lasted only seconds before reverting to the true market price. But those few seconds were enough.
Here's the attack chain:
- The attacker creates a fake price spike on a market (e.g., pushing a 15¢ market to 47.5¢ momentarily)
- During the spike, they open a leveraged position on Ultramarkets at the inflated price
- Our system executes the position at the manipulated price, borrowing vault capital to do so
- The price reverts to its actual level within seconds
- The position's health collapses immediately, triggering liquidation
- The vault closes the position at the real (much lower) price, absorbing the difference as bad debt
The attacker sacrifices their own collateral to inflict outsized damage on the vault. The difference between the fake entry price and the real exit price is the vault's loss.
Why This Was Possible
Our position opening flow validated many things: margin requirements, leverage limits, health thresholds, liquidation prices. But it did not validate whether the current spot price was consistent with recent trading history. We trusted the CLOB's reported price as ground truth.
In normal conditions, that's a reasonable assumption. Deep, well-arbitraged order books produce reliable prices. But this attack specifically targets the gap between "what the CLOB says right now" and "what the market has actually been trading at." By the time our system checked the price, the manipulation had already happened.
The Fix: Pre-Trade TWAP Guard
We shipped a fix within hours of identifying the attack pattern.
The core defense is a Time-Weighted Average Price (TWAP) service that maintains a rolling 5-minute price history for every listed market. Before any position is opened, the system compares the current CLOB spot price against this TWAP. If the spot price deviates more than a certain percentage from the rolling average, the trade is rejected.
Here's why this kills the attack:
- Ghost-fill spikes last seconds, not minutes. A 5-minute rolling average is barely affected by a momentary spike.
- The attacker needs Ultramarkets to buy at the inflated price. If we refuse to execute, the entire attack chain breaks.
- Legitimate price movements, even fast ones, don't produce 15%+ deviations from a 5-minute average.
The TWAP buffer populates from the same WebSocket price feed we already use, so there are zero additional network calls. It fills within ~15 seconds of a fresh deploy or new market listing, and trades are allowed through during the initial buffer period to avoid blocking legitimate activity on newly listed markets.
What's Next: Failed Match Monitoring
The TWAP guard is the immediate fix. The next layer we're building is real-time monitoring of failed on-chain settlements.
Hybrid CLOBs emit events when matched orders fail to settle on-chain (taker order invalidations). By subscribing to this WebSocket feed, we can detect when ghost fills are actively happening on markets we've listed. If a market shows a spike in failed settlements, we can automatically pause new position opens on that market until conditions normalize.
This is complementary to the TWAP guard. The TWAP catches the symptom (anomalous prices). Failed match monitoring catches the cause (settlement failures) and gives us an earlier signal that an attack is underway, potentially before the price deviation even hits our threshold. Together, they create two independent tripwires that an attacker would need to bypass simultaneously.
What Happened to the Attacker
We identified and banned the account. The user had $1,050 in remaining funds on the platform, which were seized under our suspicious activity policy. When the attacker attempted to withdraw, they were informed that their account had been flagged and suspended.
And this week, we're building automated detection to flag and suspend accounts exhibiting this pattern without requiring manual identification.
What This Means for Vault Depositors
The vault absorbed approximately $3,200 in bad debt from these incidents. This is reflected in the vault's NAV and, by extension, in umUSD share price. We don't obscure losses. The vault's accounting is transparent and updates in real time.
The TWAP guard is now live in production. This specific attack vector, ghost-fill price manipulation, is no longer viable against Ultramarkets. We will continue hardening the execution pipeline as new attack patterns emerge.
The Broader Context
This vulnerability is not unique to any single platform. It's a structural challenge inherent to hybrid CLOB designs that separate off-chain matching from on-chain settlement. As DeFi Rate reported, multiple traders and researchers have documented variants of this exploit since early 2026, with impacts across the ecosystem.
Building on top of shared infrastructure means inheriting some of its attack surface. Our job is to add defensive layers that protect vault capital regardless of what happens at the execution venue. That's what the TWAP guard does. We don't control the matching engine, but we do control whether we commit vault capital to a trade. Now we verify price integrity before every execution.
This is exactly what private beta is for: exposing edge cases under real conditions and hardening the system before scale. The $3,200 loss is real, and it’s reflected directly in vault NAV. We believe transparency is the only way to build durable financial infrastructure.
The TWAP guard is now live in production, and additional monitoring is on the way. This specific attack vector is no longer viable against Ultramarkets. Every incident makes the system stronger.
We’ll keep building the first Margin Layer for Prediction Markets.

Comments ()